-
Lifestyle

Lifehacker Launches Comprehensive Live Shopping Hub to Track Authentic Tech Deals and Combat Retail Hype
Lifehacker, the long-standing authority on lifestyle optimization and technological utility, has formalized its commitment to consumer advocacy through the launch…
Read More » -
Sports

Dan Skelton Secures Champion Trainer Title Amidst Record-Breaking Season and Quest for £5 Million Milestone
Dan Skelton has definitively clinched his first UK champion trainer title over jumps for the current season, a monumental achievement…
Read More » -
Entertainment

May December Breakout Charles Melton’s Ascending Trajectory Continues with "Beef" Season 2
Charles Melton, the actor whose nuanced performance in Todd Haynes’s psychosexual drama "May December" served as a significant launchpad for…
Read More » -
Entertainment

Caitlyn Jenner Writes to Donald Trump Over Passport Gender Marker Issue
Caitlyn Jenner, the Olympic gold medalist and television personality, has revealed that she penned a letter to former President Donald…
Read More » -
Entertainment

Elizabeth Matthews: Navigating the Future of Songwriting and Royalties at ASCAP
Elizabeth Matthews, the formidable leader of ASCAP, the American Society of Composers, Authors and Publishers, stands at the helm of…
Read More » -
Entertainment

The Arrest of Platinum-Selling Singer D4vd Marks a Grim Culmination in the Celeste Rivas Case
Months of clandestine hearings and mounting public speculation reached a dramatic apex Thursday afternoon with the heavily armed apprehension of…
Read More » -
Entertainment

The Crisis in Hollywood: Mayoral Candidates Clash Over Film Production Woes
Los Angeles is grappling with a significant crisis in its film and television production sector, an issue that has deeply…
Read More » -
Entertainment

Wizards Beyond Waverly Place Welcomes Back Original Cast Member Jennifer Stone for Final Season
The highly anticipated return of a beloved character has been confirmed for the upcoming third and final season of Disney’s…
Read More » -
Health & Wellness

Apple Watch Series 11 Sees Significant Price Drop as Key Health Features Debut
Apple’s latest iteration of its popular smartwatch, the Apple Watch Series 11, is currently available at a reduced price of…
Read More » -
Health & Wellness
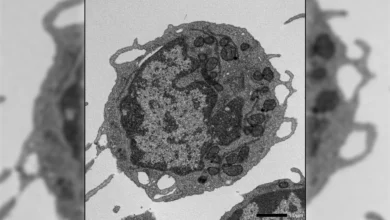
Unlocking the Secrets of Aging Blood Cells: Researchers Discover Novel Role of MLKL in Stem Cell Decline
As individuals age, the body’s intricate biological systems undergo a gradual decline, and perhaps none are as fundamental to our…
Read More »
